You can't talk security without visibility
We help growing European companies see who has access to what, which tools their teams actually use, and where their data is going.
Then we fix what needs fixing
Partnered with:




former employees can still access your systems after offboarding
more SaaS apps than IT tracks in the average 100-person company
of employees are already using AI tools their company hasn't approved
The tools are everywhere.
The visibility isn't
Growing companies have a pattern. A new tool gets adopted by one team. Then another. Then someone leaves and nobody removes their access. Then a developer starts using an AI assistant that's quietly processing customer data. Then an auditor asks for a list of every system with access to personal information.
That list doesn't exist.
We've seen this across dozens of European companies, from 30-person software houses to large manufacturing companies.
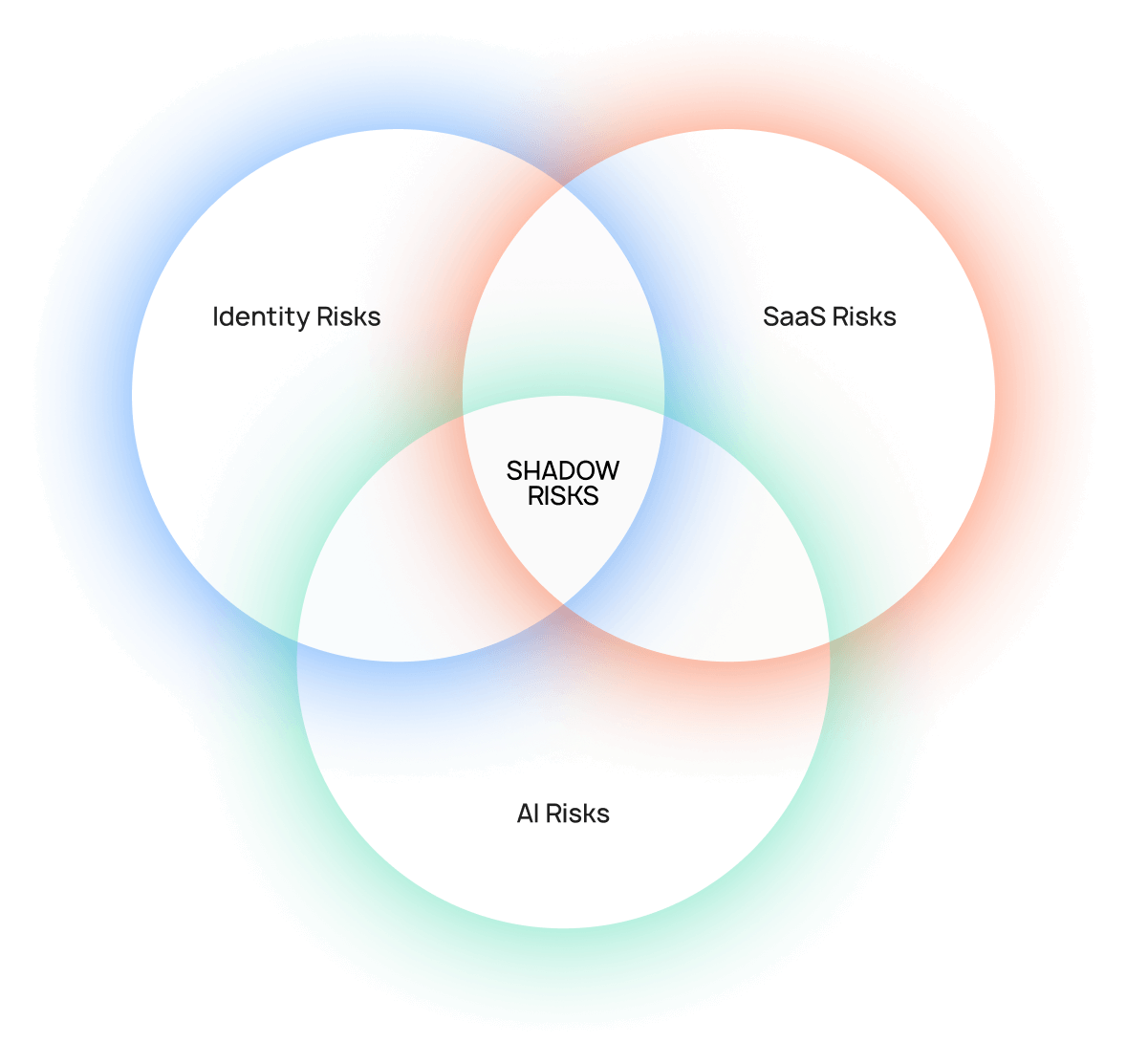
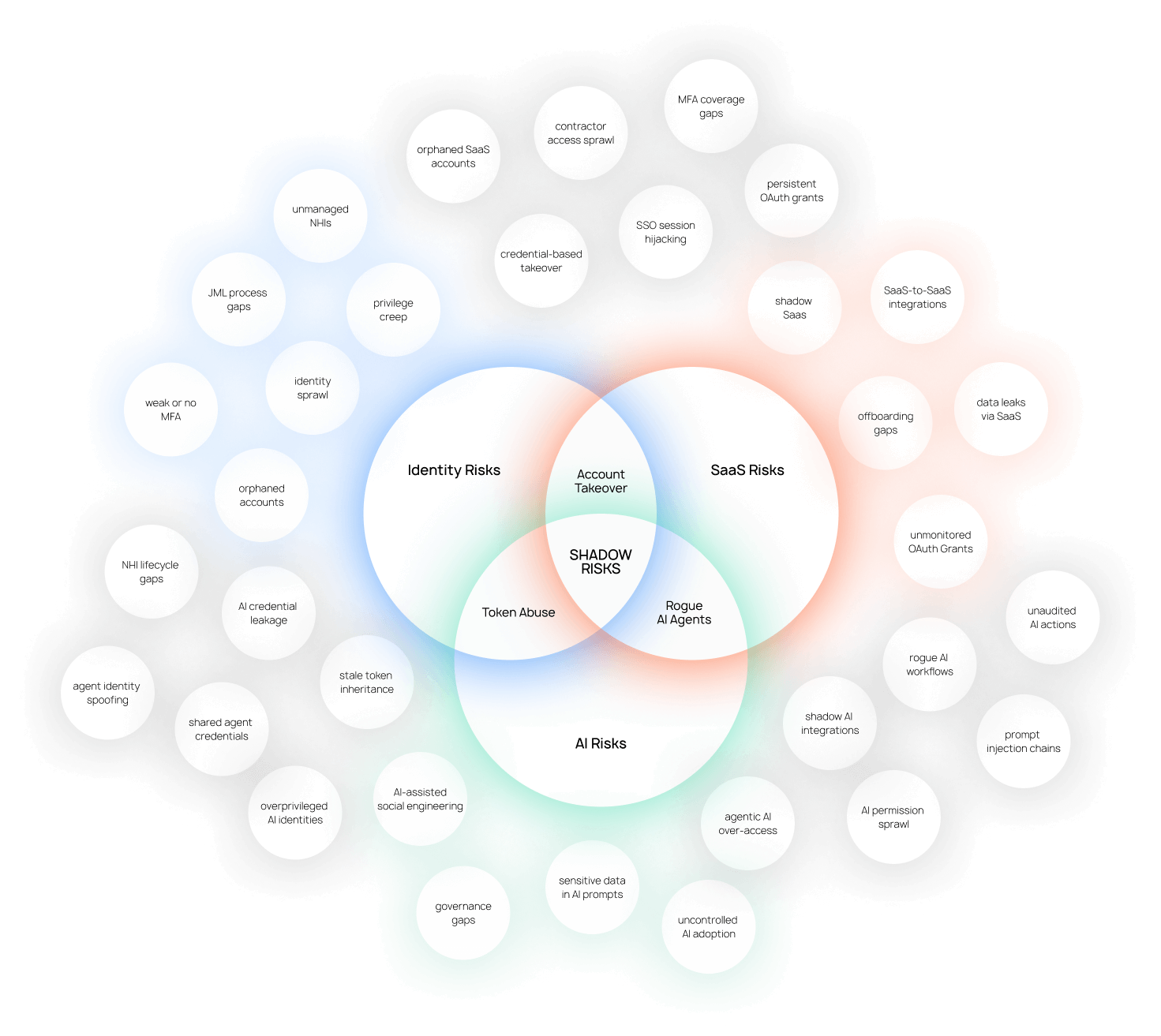
Three areas, one problem
The access chaos, the SaaS sprawl, and the AI tool risk are mostly symptoms of the same thing: the company grew faster than the infrastructure that governs it.
We work across all three because fixing one without the others doesn't hold.
You probably have more active accounts than active employees
Former contractors still in Slack. Developers with admin rights from a role they left two years ago. Offboarding that happens in HR only.
The result is that you can't answer the question any auditor or enterprise client will eventually ask: who has access to your systems right now, and why?
We map what you have, close the gaps, and put a process in place so it stays closed and fully manageable. Part of that is finding the right tools for where you actually are, not the vendors we prefer.
Typical scope:
Access audit across your full tool stack
SSO, directory and MFA setup
Joiner, mover, leaver process design
Offboarding automation
Quarterly access review cadence
Tool selection sized to your company
Your team is already using tools you don't know about
At 100 people, the average company runs 200+ SaaS tools.
IT knows about 60 of them.
The rest sit on personal cards, free tier accounts, and that recurring charge nobody can explain. Each one processing personal data is a gap in your GDPR register. Each one is a door you don't control.
We find what's there, cut what shouldn't be, and set up a process so the stack stays visible going forward. We also help you pick the right tools for the job.
Typical scope:
Full SaaS discovery and inventory
Shadow app identification and risk assessment
Tool selection matched to your size and needs
App request and approval workflow
78% of your employees are already using AI tools at work
Developers using coding assistants that pull from internal repos. Marketing pasting client briefs into ChatGPT. Support staff using tools with no data processing agreement in place.
About 27% of what goes into AI tools is sensitive information and that number doesn't drop with wider and wider AI adoption.
Banning everything doesn't work either. We've watched that play out. People use the tools anyway, just less visibly.
We map what's in use, assess where the real risk is, and build workflows that help your employees use AI correctly while you stay in control of the situation and can prevent incidents easily
Typical scope:
AI tool discovery across the organisation
Risk assessment by tool and use case
Acceptable use policy
Approved tools framework
GDPR and further compliance review
Tool selection for monitoring and governance
How many of the 17 boxes can you check?
The full map with detailed risk breakdowns across Identity, SaaS, and AI, how they connect at the intersections, and an 17-point self-assessment checklist to see where your company actually stands today.
Share it with your team. Use the checklist in your upcoming security review. Pin the map where your IT team can see it.
We know what works
We work across Identity, SaaS management and AI security tooling. We recommend what's right for each situation, but after enough implementations you develop opinions...





identity infrastructure for the AI era
Most IAM platforms were built for enterprises with dedicated IT teams and six months to implement. YeshID covers what a growing company actually needs without significant overhead to run.
.webp)

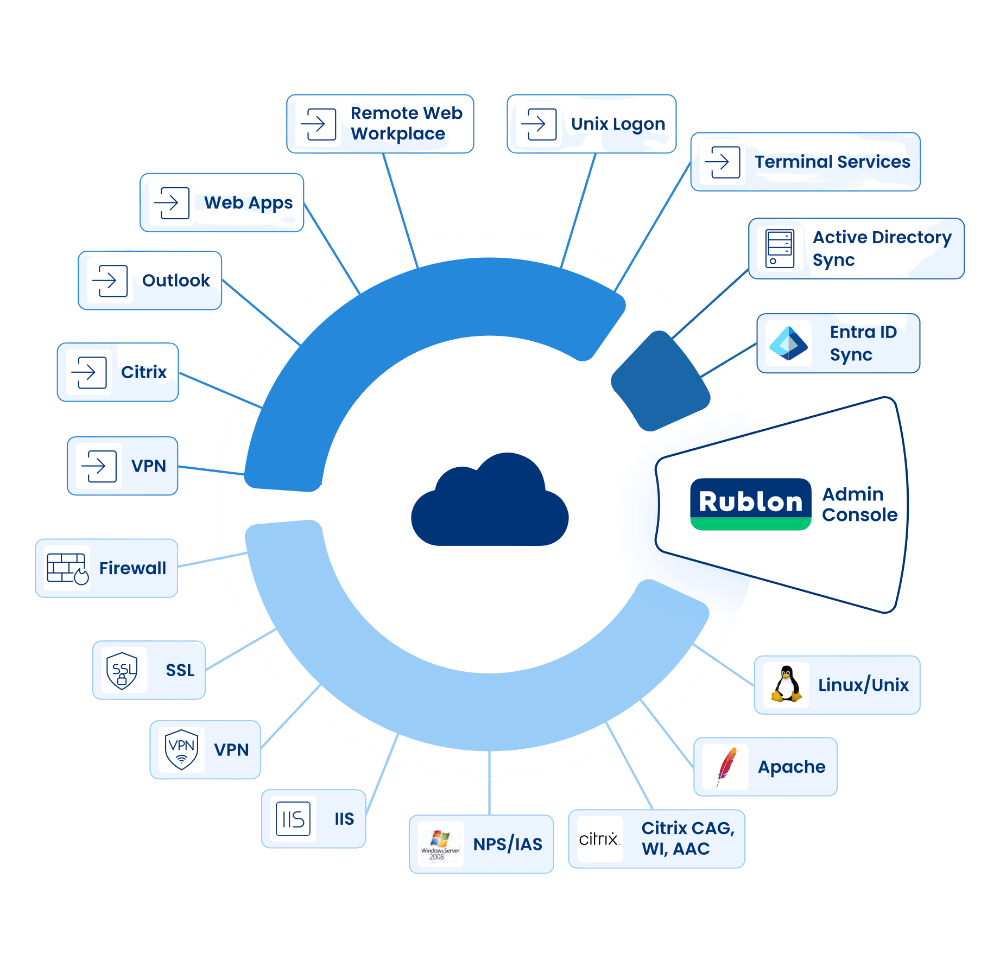
secure remote access to all technologies
Rublon is able to securely connect your users with almost any technology that they want to use.
It offers dedicated modules and software that integrates Rublon with cloud and on-premise applications using SAML, RADIUS and more.
Guides & Frameworks
Practical guides for IT teams at European companies
Zero Trust: A Modern Framework for Digital-First Companies
Remove Local Admin Rights: Balancing Security and Productivity
Identity-oriented. Practitioner-led. European.
We're Julian and Dawid. We worked in enterprise identity and access management — deploying PAM solutions, running security reviews, and explaining to boards why IAM budgets need to go up.
We kept meeting IT managers and CTOs at European companies, smart people with limited budgets, who were drowning in shadow SaaS, unmanaged AI tools, and compliance pressure.
That's why we decided to address this with unshadow, where we help keep the full spectrum of your infrastructure visible and governable.
Talk to Julian & Dawid
Most first conversations start with not quite knowing what you have or where to begin. That's normal.
Tell us what's going on and what prompted the conversation:
an upcoming audit, something that happened, a client requirement, or just a sense that things have gotten messy.
We can take it from here!


.svg.png)





