Bezpieczeństwo zaczyna się od pełnej widoczności
Pomagamy szybko rosnącym firmom lepiej zarządzać tożsamością oraz dostępami, kontrolować kto używa jakich aplikacji, oraz weryfikować, czy poufne dane nie wypływają do AI
Jesteśmy partnerami kluczowych producentów:




byłych pracowników wciąż ma dostępy do firmowych systemów po offboardingu
więcej aplikacji SaaS, niż oficjalnie wdrożonych, ma 100-osobowa firma
pracowników już teraz używa AI w codziennej pracy, mimo braku zgody przełożonych
Codziennie nowe narzędzia uzyskują dostępy do Twoich systemów, bez nadzoru
Rozwijające się firmy mają swój wzór. Nowe narzędzie zostaje przyjęte przez jeden zespół. Potem kolejny. Potem ktoś odchodzi i nikt nie usuwa dostępu. Następnie programista wdraża asystenta AI, który w tle przetwarza dane klientów. Któregoś dnia audytor prosi o listę każdego systemu z dostępem do danych osobowych.
Taka lista nie istnieje.
Widzieliśmy dokładnie taki rozwój wypadków w dziesiątkach firm - od małych startupów po duże korporacje. I ciężko jest nad tym zapanować, gdy nowe aplikacje rosną jak grzyby po deszczu, a za chwilę każda lodówka będzie miała wbudowane AI potrzebujące dostępu do maila, by "tylko śledzić zakupy". I ten dostęp otrzyma.
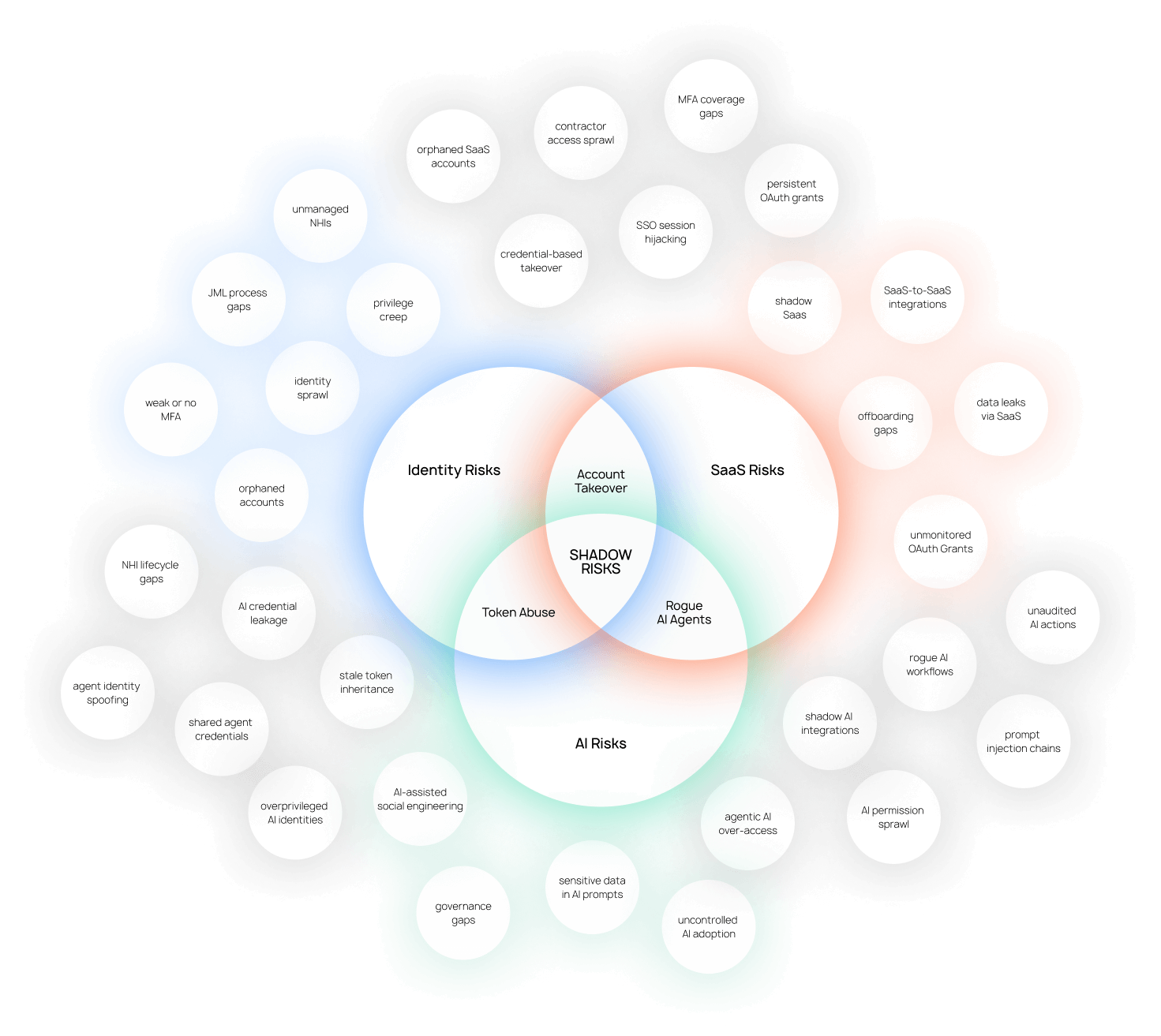
Trzy obszary, jeden problem
The access chaos, the SaaS sprawl, and the AI tool risk are mostly symptoms of the same thing: the company grew faster than the infrastructure that governs it.
We work across all three because fixing one without the others doesn't hold.
Najprawdopodobniej masz więcej aktywnych kont niż pracowników
Former contractors still in Slack. Developers with admin rights from a role they left two years ago. Offboarding that happens in HR only.
The result is that you can't answer the question any auditor or enterprise client will eventually ask: who has access to your systems right now, and why?
We map what you have, close the gaps, and put a process in place so it stays closed and fully manageable. Part of that is finding the right tools for where you actually are, not the vendors we prefer.
Typical scope:
Access audit across your full tool stack
SSO, directory and MFA setup
Joiner, mover, leaver process design
Offboarding automation
Quarterly access review cadence
Tool selection sized to your company
W Twoim systemie już teraz są aplikacje, o których nie wiesz
At 100 people, the average company runs 200+ SaaS tools.
IT knows about 60 of them.
The rest sit on personal cards, free tier accounts, and that recurring charge nobody can explain. Each one processing personal data is a gap in your GDPR register. Each one is a door you don't control.
We find what's there, cut what shouldn't be, and set up a process so the stack stays visible going forward. We also help you pick the right tools for the job.
Typical scope:
Full SaaS discovery and inventory
Shadow app identification and risk assessment
Tool selection matched to your size and needs
App request and approval workflow
78% pracowników codziennie korzysta w pracy z AI bez zgody
Developers using coding assistants that pull from internal repos. Marketing pasting client briefs into ChatGPT. Support staff using tools with no data processing agreement in place.
About 27% of what goes into AI tools is sensitive information and that number doesn't drop with wider and wider AI adoption.
Banning everything doesn't work either. We've watched that play out. People use the tools anyway, just less visibly.
We map what's in use, assess where the real risk is, and build workflows that help your employees use AI correctly while you stay in control of the situation and can prevent incidents easily
Typical scope:
AI tool discovery across the organisation
Risk assessment by tool and use case
Acceptable use policy
Approved tools framework
GDPR and further compliance review
Tool selection for monitoring and governance
Ile z 17 punktów checklisty możesz odhaczyć?
The full map with detailed risk breakdowns across Identity, SaaS, and AI, how they connect at the intersections, and an 17-point self-assessment checklist to see where your company actually stands today.
Share it with your team. Use the checklist in your upcoming security review. Pin the map where your IT team can see it.
wiemy, co działa
We work across Identity, SaaS management and AI security tooling. We recommend what's right for each situation, but after enough implementations you develop opinions...





zarządzanie tożsamością w erze AI
Most IAM platforms were built for enterprises with dedicated IT teams and six months to implement. YeshID covers what a growing company actually needs without significant overhead to run.
.webp)

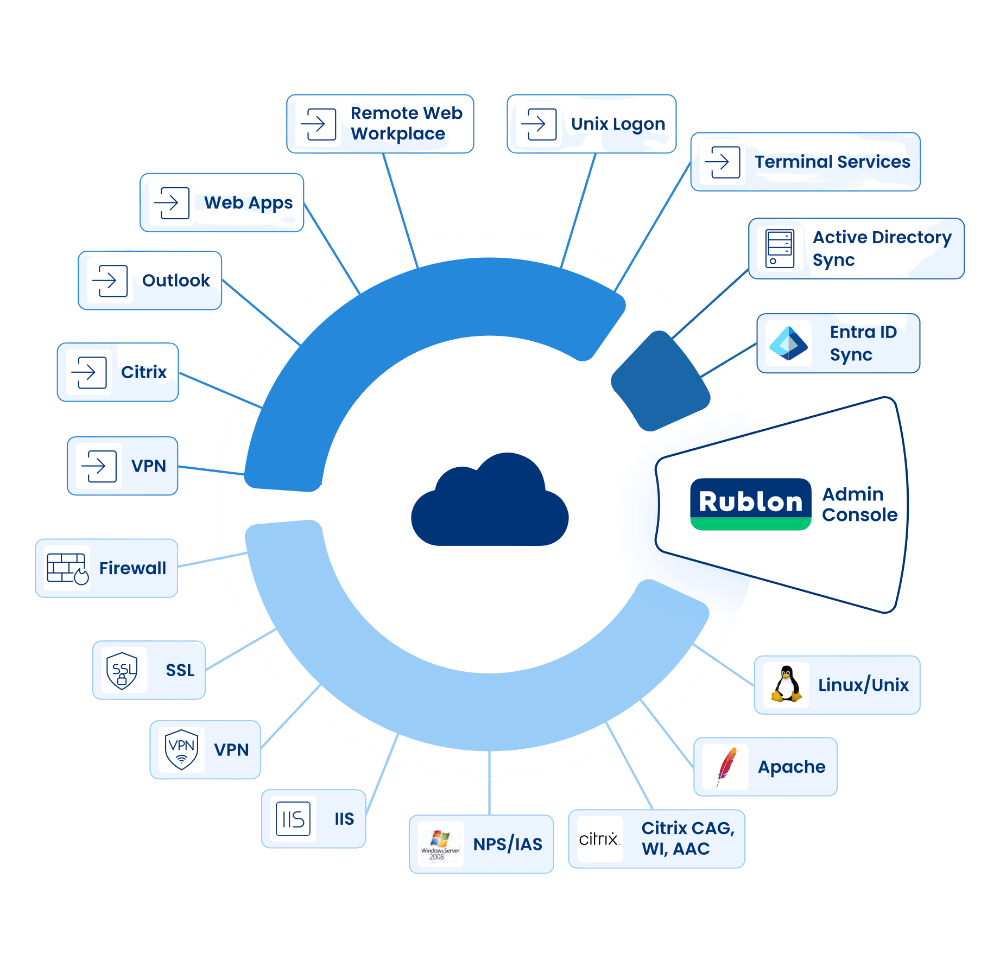
bezpieczny dostęp do każdej technologii
Rublon is able to securely connect your users with almost any technology that they want to use.
It offers dedicated modules and software that integrates Rublon with cloud and on-premise applications using SAML, RADIUS and more.
Przydatne przewodniki i artykuły
Practical guides for IT teams at European companies
Zero Trust: A Modern Framework for Digital-First Companies
Remove Local Admin Rights: Balancing Security and Productivity
Tożsamość.
Praktyka.
Europa.
We're Julian and Dawid. We worked in enterprise identity and access management — deploying PAM solutions, running security reviews, and explaining to boards why IAM budgets need to go up.
We kept meeting IT managers and CTOs at European companies, smart people with limited budgets, who were drowning in shadow SaaS, unmanaged AI tools, and compliance pressure.
That's why we decided to address this with unshadow, where we help keep the full spectrum of your infrastructure visible and governable.
Po prostu porozmawiajmy
Most first conversations start with not quite knowing what you have or where to begin. That's normal.
Tell us what's going on and what prompted the conversation:
an upcoming audit, something that happened, a client requirement, or just a sense that things have gotten messy.
We can take it from here!


.svg.png)





